To turn off and disable direct root SSH login, follow this simple tutorial:
Important
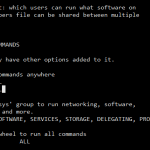
Make sure you have another account (preferably belongs to wheel user group too) which is able to login via SSH remotely, and able to SU to root user account. Else you risk been locked out from your server.
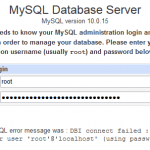
- SSH into server and login as root.
- In command shell, use pico or vi to edit sshd_config file by typing one of the following commands:
pico /etc/ssh/sshd_config
vi /etc/ssh/sshd_config
- Scroll down the SSH server configuration file and locate a line like below:
#PermitRootLogin yes
- Uncomment the line by removing the hash symbol (#), and then change the “yes” to “no”. The final line should look like below:
PermitRootLogin no
- Save the config file. In pico, press Ctrl-o, follow by Ctrl-x. In vi, type :wq and press Enter.
- Restart SSH server by typing the following command in command line, and press Enter:
/etc/rc.d/init.d/sshd restart
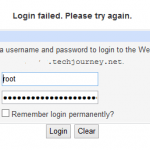
- Logout from SSH connection. Try to login as root, it should fail with Access denied error. To access root account, login with your own user name and password, and then SU to root.