Although the Malicious Software Removal Tool is basic, but it’s free, and comes installed automatically on most Windows computer if users opt-in to Automatic Updates with auto month update. Thus it’s a great tool to use to remove and delete any detectable malicious software or code that infects the computer, especially ‘first line of defense’ security protection when you don’t want to purchase a full security suites or subscribe to virus definitions/signatures update. It can also be a ‘last resort effort’ to clean up the system from specific and prevalent virus infection in case of everything else virus, Trojan, worm, root kit, malware and malicious code cleaning and deletion software fails.
But how to use Windows Malicious Software Removal Tool (WMSRT/MSRT)? The program does not have any shortcut in Start Menu nor desktop or Quick Launch area. Actually WMSRT runs in the background once every month without your knowledge, if you have installed MSRT. If you feel like running the tool to check your system manually for frequency more than once a month, or suspecting your system is infected and want to run the MSRT to clean the infection, or simply want to display view the results of the scan (by default everything is silent unless infected), you can manually execute and run the tool with the following command:
MRT.EXE
You can type this program name in command prompt, or Run command box, or in Start Search in most Windows version after Windows Vista and Windows Server 2008. Note that users must log on to the computer by using an account that is a member of the Administrators group to use the Malicious Software Removal Tool. And, user needs to give User Account Control permission to continue.
WMSRT MRT.exe supports four command line switches listed below, which is optional and most of the time not necessary unless you’re administrator for corporate network:
- /Q or /quiet – Use quiet mode. This option suppresses the user interface of the tool.
- /? – Display a dialog box that lists the command-line switches.
- /N – Run in detect-only mode. In this mode, malicious software will be reported to the user but will not be removed.
- /F – Force an extended scan of the computer.
- /F:Y – Force an extended scan of the computer and automatically clean any infections found.
Once Malicious Software Removal Tool (KB890830)’s MRT.EXE is ran, a program window is opened, where the window title also indicating the version of the tool (e.g. August 2007). If you have old version so it’s best to perform an upgrade before running the tool.
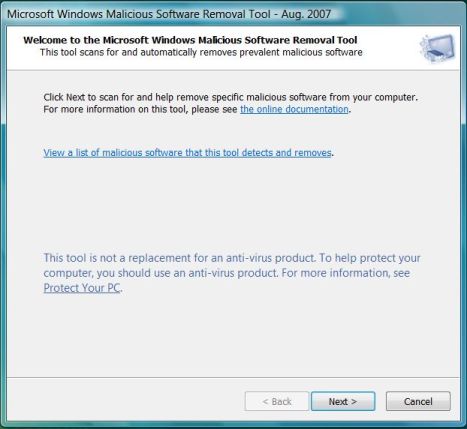
Click Next button to accept the EULA.
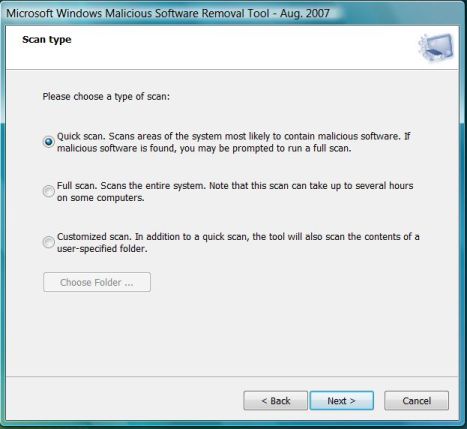
After the EULA has been accepted, the user can select a type of scan to perform. By default, Quick scan is selected, which scans computer memory and ares of system most likely infected by known malicious software and stops any malicious processes that are found. It also detects hijacked browser settings, deletes files and registry keys that are associated with processes that are identified as malicious. If malicious software is found, sometimes user may be prompted to perform a full extended scan or you may manually select to perform full scan, which scan every files and folders on all fixed and removable drives (except mapped network drivers) on the computer. Custom scan will allow users to select and customize a scan to include a specific folder and its subfolders on the computer.
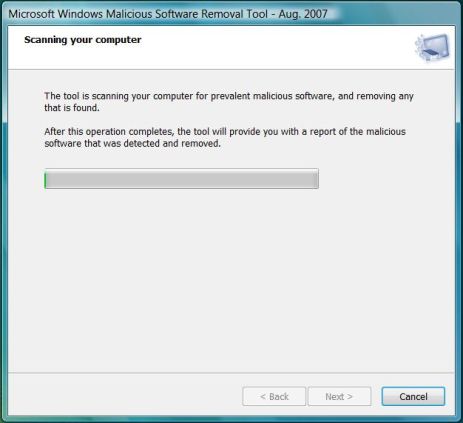
Scanning in progress. If malicious software has modified (or infected) user files on the computer, the tool will prompt you to remove the malicious software from those files. You can choose to clean specific files or all infected files found.Note that some data loss is possible during this process and that the tool may not be able to restore some files to the original, pre-infection state.
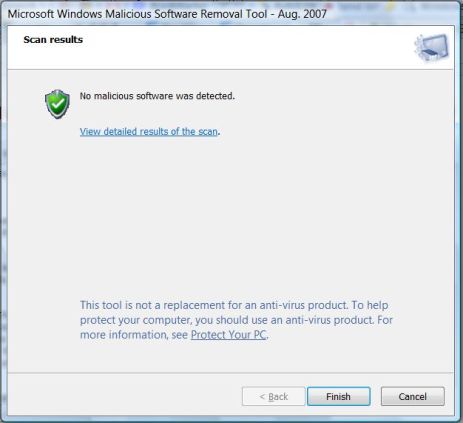
Details of results of the scan operation, unless the MRT.exe is run in quiet mode. If there is positive detection, you may also see results such as infection was found and was removed, infection was found but was not removed with suspicious files found listed, infection was found and was partially removed, computer restart required, or more manual steps.
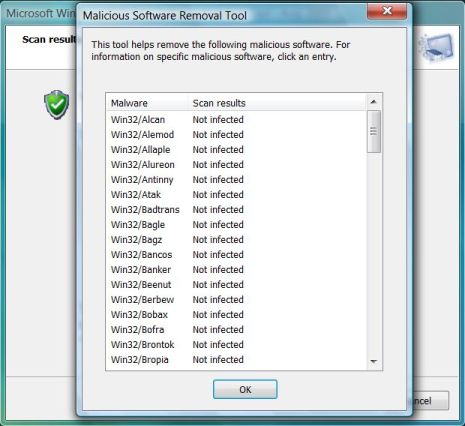
Clicking on the link “View detailed results of the scan” to view the names of different malware the tool scanned for and the results for each type.
A log file mrt.log also been created in \%WinDir%\Debug folder, and will contains following information:
Microsoft Windows Malicious Software Removal Tool v1.32, August 2007
Started On Wed Aug 29 14:46:33 2007
Results Summary:
----------------
No infection found.
Return code: 0
Microsoft Windows Malicious Software Removal Tool Finished On Wed Aug 29 16:47:30 2007
A Guided Help for KB890830 is also available to download and to run the Windows Malicious Software Removal Tool, if don’t want to run MRT.exe manually yourself. Guided Help can be downloaded here (no longer available) to show you how to use the tool step-by-step or do everything automatically.