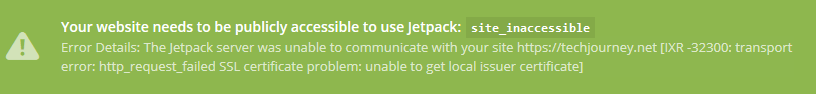
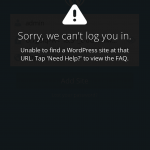
Your website needs to be publicly accessible to use Jetpack: site_inaccessible
Error Details: The Jetpack server was unable to communicate with your site https://techjournye.net [IXR -32300: transport error: http_request_failed SSL certificate problem: unable to get local issuer certificate]
In Jetpack Compatibility Test, the HTTPS self connections will return error to WP_Error object:
WP_Error Object
(
[errors:WP_Error:private] => Array
(
[http_request_failed] => Array
(
[0] => Peer certificate cannot be authenticated with known CA certificates
)
)
[error_data:WP_Error:private] => Array
(
)
)
The error indicates that there is problem with the SSL certificate installation. The most likely cause is that WordPress.com server is unable to verify the identity of the domain certificate during the TLS handshaking procedure. It may be due to either you’re using a self-signed certificate or missing root certificates (unlikely as most commonly used root CA certs is now included in web browsers and operating systems by default) and/or intermediate CA certificates bundle if you’re using trusted Certificate Authority (CA) signed digital certificate.
And end-entity domain certificate for a website is normally signed with an intermediate CA certificate from Certification Authority. The intermediate CA certificate should be installed on the web server and supplied to the client when connecting to the website. But if it doesn’t, modern web browsers will workaround it by examining the certificate for an extension named “Authority Information” which usually contain a URL to the missing intermediate CA certificates chain. The browser then fetches the missing certificates to check if they’re signed by a trusted CA, and accepts the domain certificate if it’s. However, the server on WordPress.com apparently is not able to handle the secure connection where the intermediate CA certificates are missing and not supplied by the web server.
Thus, the solution is easy. The recommended way to resolve the Jetpark SSL certificate problem is by installing the intermediate CA certificates bundle package which are supplied by the CA.
If you’re unable to install the intermediate CA certs and is using self-signed cert, another workaround is by temporarily access the WordPress admin pages via normal HTTP connection without encryption (i.e. http:// instead of https://). If you redirect all HTTP traffic to HTTPS traffic, you will need to temporarily disable the redirection. If you force the WordPress administration panel to be view over SSL via FORCE_SSL_ADMIN constant in wp-config.php configuration file, then change the value to false so that it becomes:
define('FORCE_SSL_ADMIN', false);
Once you login to WordPress admin panel /wp-admin through HTTP unsecured connection, connect Jetpack to WordPress.com, and authorize Jetpack and WordPress.com to access your WordPress blog.
Once the Jetpack connection with WordPress.com is established, you can safely re-enable the secure SSL website through HTTPS. All functions and features of Jetpack will work now even on HTTPS connection.