Many Windows Vista users install non-certified or non-signed drivers on 64-bit (x64) edition of Windows Vista, which features Kernel Patch Protection that prevents unauthorized patch or change to the key resources used by the kernel or kernel code itself and its data structures from been modified. The workaround to run unsigned and uncertified drivers in 64-bit Windows Vista is by using the following command:
bcdedit /set loadoptions DDISABLE_INTEGRITY_CHECKS bcdedit -set loadoptions \”DDISABLE_INTEGRITY_CHECK” bcdedit -set loadoptions \DDISABLE_INTEGRITY_CHECKS” bcdedit.exe -set loadoptions DDISABLE_INTEGRITY_CHECKS Bcdedit.exe /set nointegritychecks ON
However, when user attempts to run the above command to disable integrity checks on the loading drivers, the following error message appears:
An error occurred while attempting to reference the specified entry.
The system cannot find the file specified.
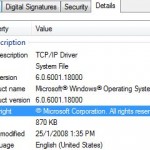
And if you manage to apply setting above previously on load options, but suddenly, there are errors and problems related to rejected or unacceptable drivers or services. Windows Vista simply does not accept any unsigned drivers or processes, causing old drivers or software processes that haven’t been updated cannot be found and installed in Vista x64. The issue is known to affect PeerGuardian, TV tuner cards, Gigabit Ethernet adapters, CD/DVD-ROM/RW drives, and many other devices. Although the devices are listed and shown in Device Manager in System Properties, but they’re not working due to the unsigned driver issue. It also affects and fails any modified system files such as patched tcpip.sys to unlock network speed potential.
In System Event Log, there may be also log message saying something like: “Windows cannot verify the digital signature for this file. A recent hardware or software change might have installed a file that is signed incorrectly or damaged, or that might be malicious software from an unknown source.”
The problem occurs because Microsoft has decided to disable DDISABLE_INTEGRITY_CHECKS support in updated x64 Windows Vista, which mean users cannot disable the integrity checks anymore. Microsoft is reportedly rolled out the change via various updates including KB932596, KB938979, KB938194 and KB941649 hotfixes, and probably Windows Vista Service Pack 1.
The updates also remove the effectiveness of ignoring code signing for drivers in Group Policy. Previously, users can run “gpedit.msc” and navigate to User Configuration -> Administrative Templates -> System -> Driver Installation, and then enable the “Code signing for drivers” and set the option to “Ignore”. This option also no longer works.
There are a few possible resolution or workaround to re-enable the ability to disable integrity checks and have DDISABLE_INTEGRITY_CHECKS option enabled so that it’s possible to load uncertified drivers or executable, such as suggestions below.
- Uninstall KB932596, KB938979, KB938194 and KB941649 updates from “Installed Updates” in “Programs and Features”, and never install them again. Best still, hide the updates from viewing and accidental install in Windows Update. After uninstalling and rebooting the computer, add the DDISABLE_INTEGRITY_CHECKS option and restart to disable integrity checks again. This method probably won’t work with the release of SP1, which incorporated all these changes.
- Press F8 key upon initial system boot up, and then choose to disable forced driver signing enforcement for that boot session. However, users have to apply this option every shutdown and restart. An easy solution to the hassle is put computer into sleep or hibernate mode instead of shutting down every time.
- Use ReadyDriver Plus to permanently disable and turn off disable driver signing enforcement automatically on every system startup.
- Sign the driver with test certificate, which is supplied with Software Development Kit (SDK) for Windows and .NET Framework Runtime Components, and then turn of test signing mode in Windows Vista x64 by using “bcdedit.exe /set TESTSIGNING ON” command. This trick will need computer running consistently in testing mode, which meant for developers to try out drivers signed with self-signed or test certificate. Risk for running computer in test signing mode is unknown, and there will be “Test Mode” watermarks been labeled on four corners of desktop, although the 64-bit desktop watermark can also be removed.