Without explanation, WordPress may suddenly start sending malicios spam emails which appeared to be originating from a PHP script used by WordPress.
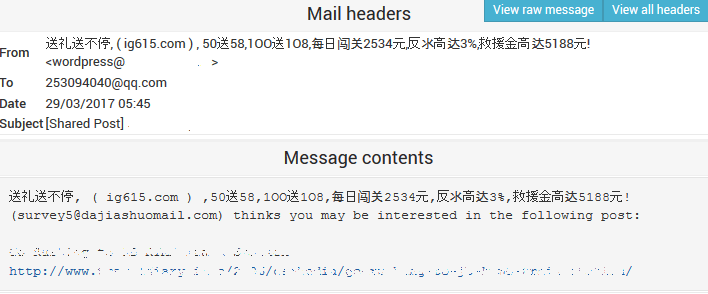
All the emails automatically and discreetly sent by WordPress has some common characteristics. All the emails has the subject starting with [Shared Post] <Title of the Post / Page>. The content of the emails contains some spamming message (which mostly in Chinese language for now), and then following by the following lines:
([email protected]) thinks you may be interested in the following post:
<Title of the Post / Page>
<URL of the Post / Page>
The spam emails are currently targeted at mailboxes of Chinese email accounts, mainly qq.com, 163.com, vip.sina.com, sohu.com, kk.com, 126.com, 163.net, qq.om, pp.cm, raz.com.cn, 253com.cn, 139.com, yeah.net, jiom.com, 123.com, sogou.com, m165.com, fxmail.com, 1234.com, 193.com, qq.cn, qzone.qq.com and many more, including invalid domains.
The hidden delivery of spam email messages can be viewed from the maillog. As more and more spam emails been rejected, bounced, or failed delivery, the mail queue of the mail server is getting longer and longer, directly raising sign of warning.
However, if you running malware check on the WordPress website using various security plugins such as Wordfence Security, Sucuri Security, Anti-Malware Security and Brute-Force Firewall, Quttera Web Malware Scanner, iThemes Security, AntiVirus and etc. to scan and detect any exploits, malware and spam injections or hacking attempts, chance is that these security plugins will return a clean result – no malicious script, no injected code, no hacking attempt.
Upon investigating the access log of web server, it appears to be hackers or bots who have been constantly sending HTTP/HTTPS requests to Jetpack Sharing feature to share a post or page via email.
106.110.35.221 - - [22/May/2017:10:20:54 -0500] "POST /?share=email&nb=1 HTTP/1.1" 302 - "http://techjourney.net/?share=email&nb=1" "Mozilla/4.0 (compatible; MSIE 9.0; Windows NT 6.1)" 106.110.35.221 - - [22/May/2017:10:20:54 -0500] "GET /?shared=email HTTP/1.1" 200 33972 "http://techjourney.net/?share=email&nb=1" "Mozilla/4.0 (compatible; MSIE 9.0; Windows NT 6.1)" 183.143.51.57 - - [22/May/2017:10:20:55 -0500] "POST /?share=email&nb=1 HTTP/1.1" 302 - "http://techjourney.net/?share=email&nb=1" "Mozilla/4.0 (compatible; MSIE 9.0; Windows NT 6.1)" 183.143.51.57 - - [22/May/2017:10:20:56 -0500] "GET /?shared=email HTTP/1.1" 200 33972 "http://techjourney.net/?share=email&nb=1" "Mozilla/4.0 (compatible; MSIE 9.0; Windows NT 6.1)"
The share via email of Jetpack Sharing has a vulnerability which allows spammers or spam bots to send spam through it. Before the loophole is fixed, use one of the following resolutions to stop the spam.
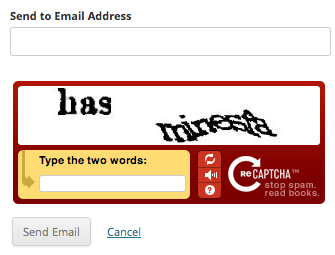
Method 1: Implement reCaptcha for Email Sharing Button
- Register for an account at Google reCaptcha to get a Public and a Private key.
- Open the site’s wp-config.php file, and add the following constants with both reCaptcha keys right before the line of “/* That’s all, stop editing! Happy blogging. */”
define( 'RECAPTCHA_PUBLIC_KEY', 'XXXXXXX' ); define( 'RECAPTCHA_PRIVATE_KEY', 'XXXXXXX' );
Now, everybody has to pass the reCaptcha verification before sending an email, which will eliminate the spams been sent from your web host.
Method 2: Effective Captcha-Less Anti-Spam Plugin
If you’re not a fan of Captcha, there are several Captcha-less anti-spam WordPress plugin that can help to eliminate email spams origination from your web server. We like WP-SpamShield Anti-Spam for its effectiveness, though some other plugins such as Spam protection FireWall, AntiSpam by CleanTalk, Anti-Spam, Antispam Bee, WordPress Zero Spam and many more may also do the job.
Method 3: Disable the Email Sharing Button
You can remove the Email Sharing button from Jetpack Sharing buttons, which effectively disable share by email feature. To remove the Email Sharing button, go to Settings -> Sharing in your WordPress dashboard.
Method 4: Disable Sharing Feature of Jetpack
Disable the Sharing in Jetpack’s Settings will stop allowing spammers to use email sharing feature to send out email spams.
Method 5: Disable Jetpack Plugin
A drastic measure, for those who are worried about the security of Jetpack, which will disable all features of Jetpack, and with it, fixes all vulnerabilities the come with the plugin.
Method 6: Block the Spammers’ or Bots’ IP Address in Firewall
You can retrieve the IP addresses which sent the requests to email sharing button via web server’s access log. Arm with the list of IP addresses, it’s possible to configure the firewall to block all connections from the IP addresses.
Method 7: Route the Website through CloudFlare
CloudFlare uses collective intelligence to stop online threats range from nuisances like comment spam and excessive bot crawling to malicious attacks like SQL injection and denial of service (DOS) attacks. It should be able to notice the attack pattern and block it. Else, you can also create rules to block such request connections from hitting your server.